For most folks, emojis are an innocent way to avoid typing, but there’s nothing innocent about the way denizens of the online underworld are using them, according to threat intelligence company Flashpoint.
As threat actor activity continues to shift toward informal, fast-moving communication platforms such as Telegram and Discord, the way adversaries communicate is evolving, Flashpoint explained in a company blog. Emojis, often dismissed as casual or nontechnical, have become a meaningful part of that evolution.
Across illicit forums, messaging apps, and closed communities, emojis are used not just for expression, but for signaling intent, categorizing activity, and, in some cases, obscuring meaning from outsiders.
“What we’re seeing across illicit communities is that emojis are being used as a consistent signaling layer alongside text,” Flashpoint’s National Security Solutions Training Director Alanah Crocker said in a statement.
“They indicate things like access, monetization, targeting, and success in a way that’s fast, repeatable, and often easier to scale across languages,” she added.
Influence of Telegram and Discord
Platforms like Telegram and Discord have changed how threat actors communicate. “Telegram and Discord are giving threat actors encrypted, high-velocity, ephemeral channels with global reach and minimal moderation — something malicious actors have never had,” explained Yagub Rahimov, CEO of Polygraf AI, an enterprise AI security company in Austin, Texas.
“Communication has shifted from structured dark web forums to fast-moving environments where traditional monitoring breaks down,” he told TechNewsWorld. “To many, it is data sovereignty, but for those nation states and other threat actors, it is freedom to damage.”
“The shift to platforms like Telegram and Discord has fundamentally changed how threat actors communicate because these environments are fast, semi-anonymous, and optimized for real-time coordination,” observed Ensar Seker, CISO of SOCRadar, a threat intelligence company in Newark, Del.
“In these channels, actors operate more like agile teams than traditional forum users, and emojis become a natural extension of that — lightweight, language-agnostic, and instantly recognizable across global groups,” he told TechNewsWorld. “This reduces friction in multilingual ecosystems and allows threat actors to coordinate operations at speed without relying on long-form text.”
How Emojis Help Evade Detection
Threat actors primarily gravitate toward Telegram because it offers the anonymity that Signal provides, along with the community that traditional forums once provided, said Karen Walsh, CEO of Allegro Solutions, a cybersecurity consulting company in West Hartford, Conn.
“While it’s easy to forget, threat actors are people, just with malicious intent,” she told TechNewsWorld. “They use emojis to communicate an idea the same way legitimate users do.”
For example, she continued, in online communities like TikTok, legitimate users have gotten around keyword filters for Palestine by using the watermelon emoji that has the same color as the Palestinian flag. Initially, only some people understood this use until it became ubiquitous across all apps.
“Similarly, threat actors are using these images to subvert keyword detection by creating a visual shorthand that ‘insiders’ will know,” she said. “As images, the keyword filters will not recognize them, giving threat actors another way to evade detection. Meanwhile, they also create a sense of community and an unspoken code of belonging within this social group.”
SOCRadar’s Seker explained that traditional monitoring systems rely heavily on text matching, but substituting or augmenting keywords with emojis can break those models. “A phrase that would normally trigger an alert can be rendered invisible or benign-looking simply by replacing key terms with symbols,” he said.
Walsh added that using images to highlight important information reflects how people read digital content. “Most people skim information on the internet, and research proves that people read differently on the internet than they do in hardcopy print,” she explained. “The colors, shapes, and offset formatting of emojis further enable this, making the important information easier to find when skimming the content.”
Emoji as Protocol
Emojis serve as compressed operational shorthand — a kind of secret communication. “Among the most used keywords we see today are key emoji signaling stolen credentials, a money bag confirming payouts, and country flags designating targets,” noted Polygraf’s Rahimov.
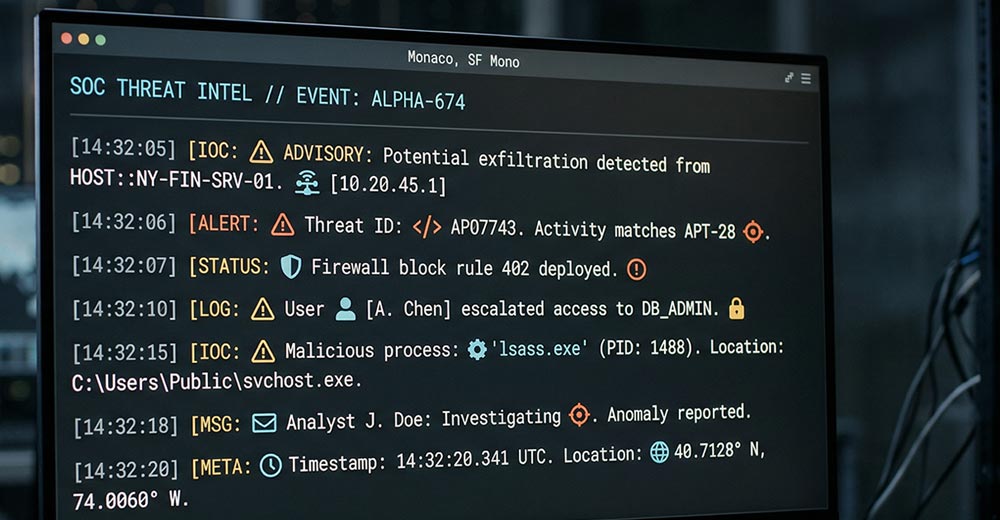
“In the DISGOMOJI campaign, a Pakistan-linked APT group used emojis as literal machine commands — a camera emoji captured screenshots, a fire emoji exfiltrated files, a skull terminated processes,” he said. “This was not slang. It was a lightweight protocol.”
“Emojis are low-entropy encoding that hides in plain sight,” he continued. “Often, you would not even think that it means something. When a threat actor replaces ‘stolen credit card’ with a card emoji layered over multilingual slang, regex-based filters see nothing actionable. Security tools built to scan for string-based commands simply become blind.”
Emojis are increasingly used as shorthand to signal intent. “A single icon can indicate stages of an operation, such as targeting, exploitation, or monetization, without explicitly stating it,” Seker explained. “Certain symbols may imply ‘access available,’ ‘credentials for sale,’ or ‘operation successful,’ enabling actors to communicate sensitive meaning in a compressed and less detectable form.”
“Threat actors also use emojis to categorize activity streams within busy channels,” he added. “In high-volume Telegram groups, specific emojis can function like tags, separating malware discussions from data leaks, initial access offers, or financial fraud. This creates a visual taxonomy that allows participants to quickly filter relevant information without structured indexing.”
Ambiguous Meaning
From an obfuscation perspective, emojis introduce ambiguity that is difficult for automated systems to interpret. “The same symbol can carry different meanings depending on context, community, or even the specific threat actor group,” Seker explained. “This contextual variability makes it harder for outsiders and detection systems to accurately understand the intent behind the communications.”
“This reminds me of the saying ‘A picture is worth a thousand words,’” added Mark Odom, a senior solutions engineer at Black Duck Software, an applications security company in Burlington, Mass.
“The same applies for an emoji,” he told TechNewsWorld. “Based on context, an emoji can represent many things, such as meaning, status, or intent. An emoji depicting a key may represent something harmless in one conversation, such as someone simply forgetting a house key. In another context, perhaps it is referring to a list of credentials.”
Another consideration is a chain of emojis, he added. “If a picture is worth a thousand words, how many words does a chain of pictures represent?” he asked. “Even knowing what a threat actor intends, how would law enforcement, for instance, go about proving that intent without simple-worded messaging? It adds not only to the complexity of locating the conversations but also what might be required to prove the intent.”
“In terms of using patterns to locate threat actors,” he continued, “you can’t rely on emojis alone as a valid method for isolating these types of conversations. Threat actors might include words along with the emojis in some cases, such as ‘selling’ before an emoji to indicate intent, which could help, but this still doesn’t increase the reliability of any results when thinking of a massive amount of data.”
Emoji Dialects
Nevertheless, Rahimov argued that threat intelligence teams need to treat emoji patterns as behavioral signatures and use contextual tools. “Essentially speaking, contextual behavior is the main weapon defenders have, since aliases can change but behaviors remain,” he said.
“Usage patterns can actually become a signal in itself,” Seker added. “Over time, specific groups develop consistent ’emoji dialects’ that can be tracked. Analysts can use these patterns as part of behavioral fingerprinting, correlating activity across platforms, attributing campaigns, or identifying returning actors even when usernames or infrastructure change.”
“The use of emojis reflects the professionalization of cybercrime ecosystems,” he said. “These actors are optimizing for efficiency, scale, and resilience, just like legitimate organizations.”
“Emojis are not a novelty,” he warned. “They are becoming part of the operational language of modern threat actors, and defenders need to treat them as such.”
Read the full article here